DevSecOps Continuous Monitoring: Vigilance Across the Lifecycle
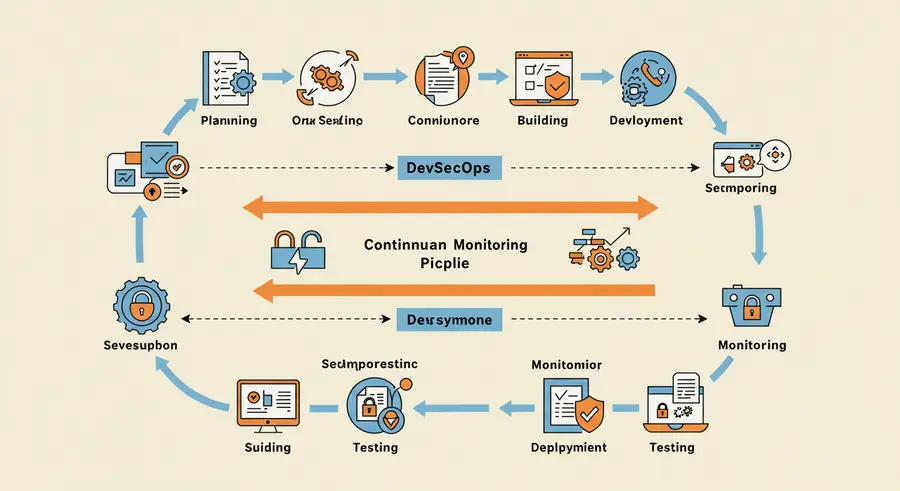
In the dynamic world of software development, simply building security into the initial stages of the pipeline is no longer enough. The threat landscape evolves rapidly, and applications, once deployed, continue to present new attack surfaces. Continuous monitoring is the practice of maintaining constant vigilance over your applications and infrastructure throughout their operational lifespan, ensuring that security remains an ongoing, adaptive process rather than a static checkpoint.
What is Continuous Monitoring in DevSecOps?
Continuous monitoring involves the systematic and automated collection, analysis, and reporting of security-related information. It extends beyond the build and deployment phases, encompassing runtime environments, user activity, configuration changes, and external threat intelligence. The goal is to proactively identify and respond to security threats, vulnerabilities, and misconfigurations in real-time or near real-time, minimizing the window of exposure and potential impact of breaches.
Key Aspects and Components
Implementing effective continuous monitoring requires a blend of technology, process, and people:
- Log Management and SIEM: Centralized collection and analysis of logs from all layers of the application and infrastructure stack.
- Runtime Application Self-Protection (RASP): RASP technologies integrated directly into the application runtime environment, providing self-protection capabilities.
- Infrastructure as Code (IaC) Scanning: Continuously scanning your IaC definitions for security misconfigurations and compliance violations.
- Cloud Security Posture Management (CSPM): Tools that continuously monitor cloud environments for misconfigurations, compliance deviations, and security risks.
- Vulnerability Management: Ongoing scanning of applications and infrastructure for known vulnerabilities, coupled with automated patching and remediation workflows.
- Threat Intelligence Integration: Incorporating real-time threat intelligence feeds to inform monitoring systems about emerging threats.
- Performance and Security Analytics: Leveraging advanced analytics and machine learning to identify subtle patterns, similar to how AI-powered market intelligence detects anomalies in financial data.
Conclusion: A Non-Negotiable Pillar of DevSecOps
Continuous monitoring is not merely a feature of DevSecOps; it's a fundamental requirement for building secure, resilient, and compliant software in today's digital age. By embracing this proactive and pervasive approach to security, organizations can navigate the complexities of modern cyber threats with confidence.